3 结论
从本体角度出发建立了HDDoS的概念化模型,总结了HDDoS防御研究所涉及的各个方面。提出一种基于离群数据挖掘的HDDoS防御策略,通过实验证明了该方法的有效性。
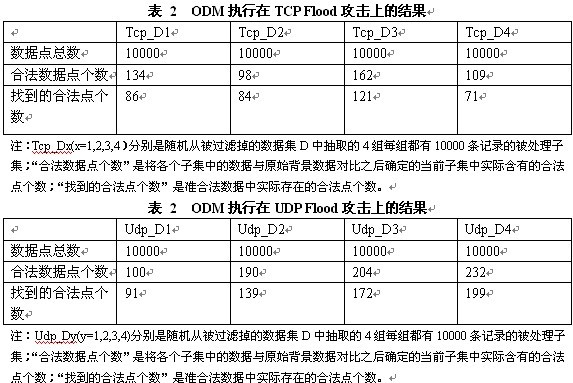
实验表明,ODM方法可保障遭受大流量DDoS攻击的系统除受攻击服务外正常运行;可逐渐恢复受攻击服务的运行;ODM方法运用离群数据挖掘算法很好地解决了过滤产生的间接伤害难以恢复的问题。
作者简介:王冬琦(1982—),男,博士,东北大学信息学院计算机系统结构研究所,研究方向:信息网络安全;郭剑锋,男,硕士,总工程师,辽宁省信息安全与软件测评认证中心,研究方向:信息网络安全管理;常桂然,男,教授,博士导师,东北大学信息学院计算机系统结构研究所,研究方向:网络与协同计算技术,网络信息安全技术,分布式多媒体系统。
参考文献
[1] Hyunsang Choi, Heejo Lee*, Hyogon Kim. Fast detection and visualization of network attacks on parallel coordinates [J]. Computers & Security, 2009, 28(5): 276-288
[2] Jong Sou Park,Khaja Mohammad Shazzad,Dong Seong Kim. Toward modeling lightweight intrusion detection through correlation-based hybrid feature selection [C]. First SKLOIS Conference,CISC2005.Proceedings. Beijing,China:Infromation Security and Cryptology, 2005. 279-289
[3] Gavrilis Dimitris, Tsoulos Ioannis, Dermatas Evangelos. Feature Selection for Robust Detection of Distributed Denial-of-Service Attacks Using Genetic Algorithms[J]. Methods and Applications of Artificial Intelligence, 2004, 3025: 276-281
[4] 徐图,何大可. 网络流单边连接密度的时间序列分析[J]. 四川大学学报(工程科学版),2007,39(3): 136-140
[5] 程光,龚俭,丁伟. 基于抽样测量的高速网络实时异常检测模型[J]. 软件学报, 2003, 14(3):594-599
[6] Yang Xiang, Wanlei Zhou. Intelligent DDoS Packet Filtering in High Speed Network[C]. 3rd International Symposium on Parallel and Distributed Processing and Applications. Nanjing, China:ISPA 2005,2005. 395-408
[7] Xie Yi, Yu Shun-zheng. A novel model for detecting application layer DDoS attacks [C]. First International Multi- Symposiums on Computer and Computational Sciences, IMSCCS'06. Hangzhou, Zhejiang, China:First International Multi- Symposiums on Computer and Computational Sciences, IMSCCS'06, 2006.56-63
[8] Jungtaek Seo, Cheolho Lee, Taeshik Shon,et al. A New DDoS Detection Model Using Multiple SVMs and TRA[J]. Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), 2005, 3823 LNCS: 976-985
[9] 高能,冯登国,向继. 一种基于数据挖掘的拒绝服务攻击检测技术[J]. 计算机学报,2006,29(6): 944-951
[10] 曲海鹏,冯登国,苏璞睿. 基于有序标记的IP包追踪方案[J]. 电子学报,2006,34(1):173-176
[11] S. Savage, D. Wetherall, A. Karlin, and T. Anderson[J]. Computer Communication Review, 2000, 30(4):295-306
[12] D. Dean, M. Franklin, and A. Stubblefield. An algebraic approach to IP Traceback[J]. CM Transactions on Information and Systems Security, 2002, 5(2):119-137
[13] 魏军,连一峰,戴英侠,李闻,鲍旭华. 一种基于路由器矢量边采样的IP追踪技术[J]. 软件学报,2007,18(11):2830-2840
(责任编辑:adminadmin2008)